As cybersecurity experts have observed, modern malware like ransomware, keyloggers, banking trojans, and cryptojackers generates substantial revenue for attackers. To maximize profitability amid rising threats and effective free antivirus solutions that often outperform paid ones, developers engineer resilient code.
Hackers employ sophisticated evasion techniques against antivirus software, which traditionally relies on signatures—unique digital fingerprints—to identify threats. Once a new malware variant is detected, its signature is shared across antivirus databases, alerting systems worldwide to block it.
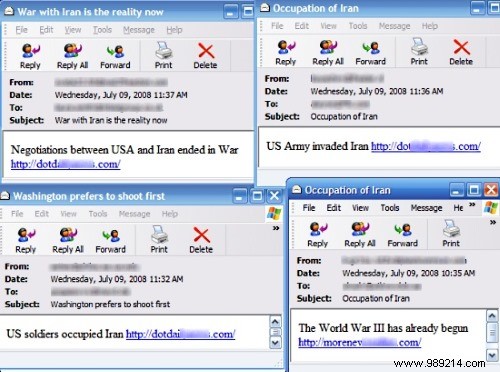
A real-world example is the Storm Worm, a polymorphic malware that emerged in 2007. It spread via emails with subjects like "230 dead as storm hits Europe." After infection, it mutated every 30 minutes, altering email subjects while preserving its core functionality.
Metamorphic malware takes evasion further. Unlike polymorphic variants with detectable core code, metamorphic engines completely rewrite the malware's structure with each iteration. They maintain identical logic and capabilities but insert junk code, reorder functions, and restructure to create entirely new signatures, making detection far more challenging.
In the escalating arms race between malware creators and defenders, AI plays a pivotal role on both sides.

AI empowers polymorphic and metamorphic malware by enabling rapid, efficient code mutations, resulting in stealthier variants that spread wider and dodge more defenses.
Fortunately, leading security firms leverage advanced AI for behavior-based detection. These systems analyze runtime actions rather than static signatures, identifying and quarantining threats dynamically based on suspicious behaviors.
While advanced evasion tactics may seem daunting, the strongest defense remains user vigilance. Avoid downloading unverified files, opening suspicious emails, or clicking dubious links—even from contacts. Without an entry point, no malware can infect your system.
As antivirus tools proliferate, malware evolves to counter them. Armed with knowledge of polymorphic and metamorphic techniques, you're better equipped to stay secure.
Will morphing malware outpace defenses, or will AI-driven security prevail? Share your thoughts in the comments.
Image source: Cybercrime Wiki