Code injection, also known as remote code execution (RCE), happens when attackers inject malicious code into an application, exploiting unvalidated user inputs. This can breach data security, corrupt databases, steal sensitive information, or bypass authentication—common in apps that process user data without proper checks.
Contents: Types of Code Injections, How SQL Injections Work, What SQL Injection Can Do, How to Prevent SQL Injections, Script Injection, How to Prevent Script Injections, Conclusion
Apps are most vulnerable when executing code without input validation. Consider this example of risky code:
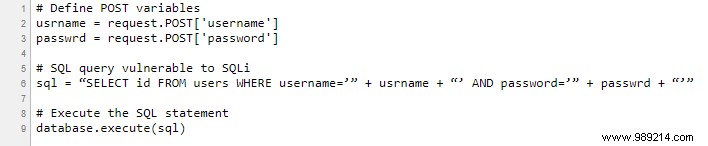
Here, an attacker could inject a payload like:
password’ OR 1=1
This alters the query executed by the database server to:
SELECT id FROM users WHERE username='username' AND password='password' OR 1=1
SQL injection is the most common code injection attack. Since SQL powers data manipulation in relational databases (RDBMS), attackers can execute arbitrary SQL to access, alter, or delete data. Impacts include bypassing logins, exposing sensitive info, undermining data integrity, and enabling fraudulent transactions or balance changes.
Assume all user input is malicious. Follow these proven steps from cybersecurity best practices:
Script injection, often called Cross-Site Scripting (XSS), lets attackers embed malicious scripts into web forms on data-driven sites via UI elements. Common targets include <script>, <meta>, <html>, <body>, <embed>, <frame>, <frameset>, and <img> tags.
Tailor defenses to your tech stack, but core principles include:
Prevention beats remediation. As tech evolves, threats multiply—stay protected with timely patches, updates, and best practices to minimize code injection risks.