Introduced in macOS in 2007 and mandated for App Store apps by 2012, sandboxing is a core security feature that confines potentially compromised applications. As Apple explains, "While App Sandbox does not prevent attacks on your app, it minimizes the damage a successful attack can cause." By isolating apps, macOS sandboxing significantly reduces risks to your system and data.
Each app operates within its own isolated "sandbox"—a restricted environment for reading and writing files. To access resources outside this boundary, the app must request explicit permission from the operating system. The OS grants the minimum necessary access with limited details, adhering to the principle of least privilege.
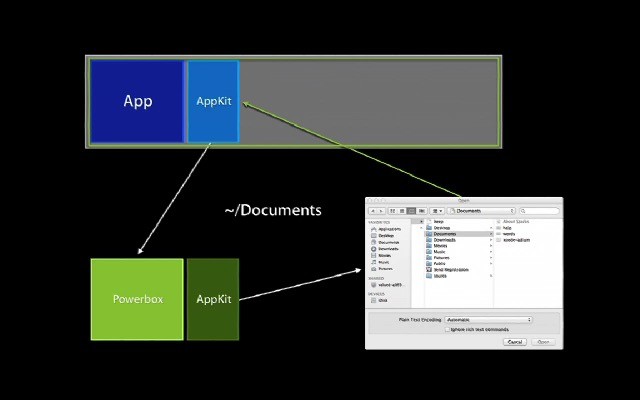
For example, when selecting files via the Powerbox file picker, the app gains access only to the chosen files without visibility into their full paths or directory structures. This enables essential functions like file opening while blocking broader risks.
This is enabled by entitlements like com.apple.security.files.user-selected.read-write. Developers declare these upfront, and macOS enforces strictly limited capabilities based on them. The entire model revolves around apps stating their intentions and receiving supervised permissions for sensitive operations.
Since June 1, 2012, all third-party apps on the Mac App Store must be sandboxed. While this supports robust functionality, App Store versions are often more restricted than direct downloads. Many developers offer dual versions: a full-featured one outside the Store and a sandboxed variant for distribution benefits.
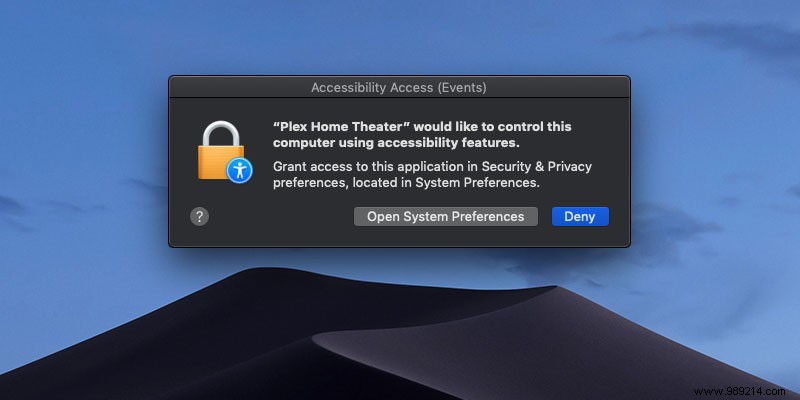
Sandboxing adds development complexity, making new features harder to implement—if permitted at all. It pairs well with App Store perks but requires user-granted extensions like accessibility permissions.
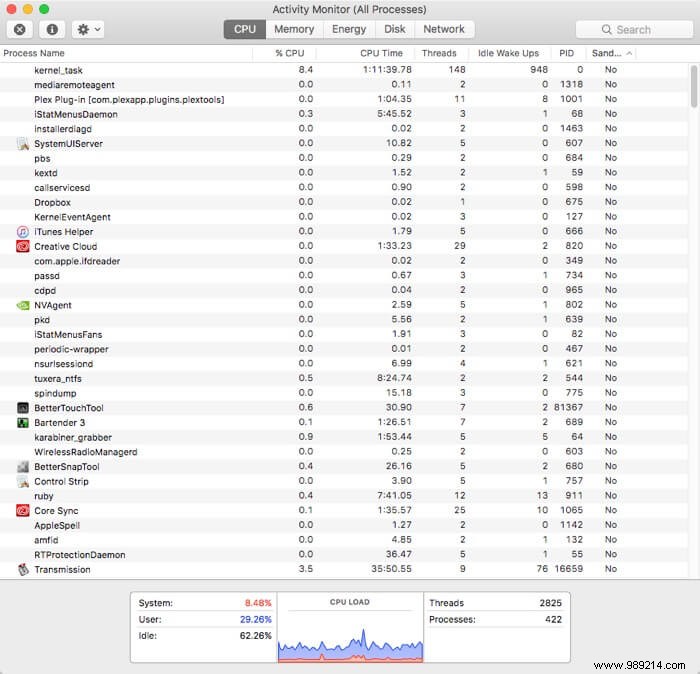
To check if your apps are sandboxed, launch Activity Monitor, right-click column headers, and add the "Sandboxed" column.
However, sandboxing isn't universal. Apps requiring deep system integration, inter-app communication, or global monitoring—like TextExpander for system-wide shortcuts—can't fully operate within it, limiting innovative workflows.
As a seasoned macOS power user with years of experience managing app ecosystems, I've seen sandboxing's promise tempered by its rigidity. It bolsters security but can hinder the speed and advanced features that define top Mac apps like TextExpander, Snagit, and TotalFinder—none of which I run sandboxed daily. Future safeguards must balance protection with flexibility, transparency, and power to avoid widespread workarounds.
Image credit: Apple