Don't be fooled by the whimsical name "Pretty Good Privacy." PGP encryption remains the gold standard for secure communication, trusted by activists, journalists, and professionals since 1991. While the underlying math is sophisticated, the core idea is straightforward: only the right key unlocks the message.
Contents
How does it work?
What can I use PGP encryption for?
How do I get started?
Conclusion
Picture sending a confidential letter where only the recipient can read it. Simply coding the message won't suffice if the key travels with it—interceptors could crack it.
PGP solves this with asymmetric public-key cryptography. Each user has a pair: a public key shared freely and a private key kept secret. The magic is one-way encryption: data encrypted with the public key can only be decrypted by the matching private key.
Here's the process in action:
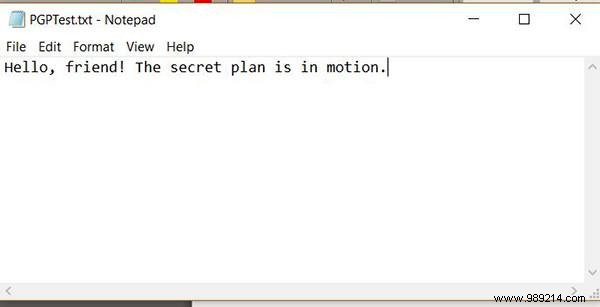
1. Compose your message.
2. Encrypt it using the recipient's public key.

3. Send the encrypted message—interceptors see only gibberish.
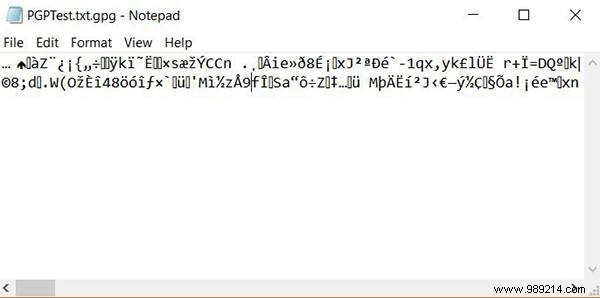
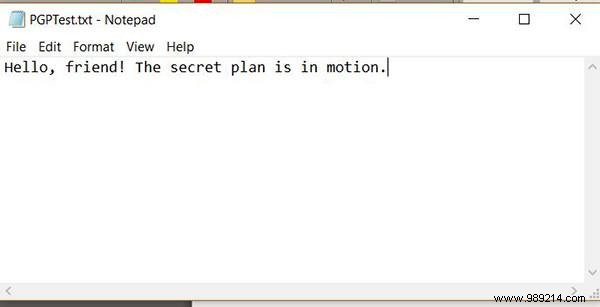
4. The recipient decrypts it with their private key, revealing the original text.
This is a simplified overview. For deeper technical details, consult established cryptography resources.
PGP shines for encrypting emails—tools like Thunderbird with Enigmail make it seamless. Its versatility extends to any text, files, folders, or drives. Journalists publish public keys for secure tips from sources, while it's also employed in high-stakes privacy scenarios.
Generating your key pair is straightforward, no cryptography PhD required. We'll use proven, free tools like Gpg4win for Windows (GPG Suite for Mac, native on Linux).
1. Download Gpg4win, a robust, open-source suite (donations welcome).

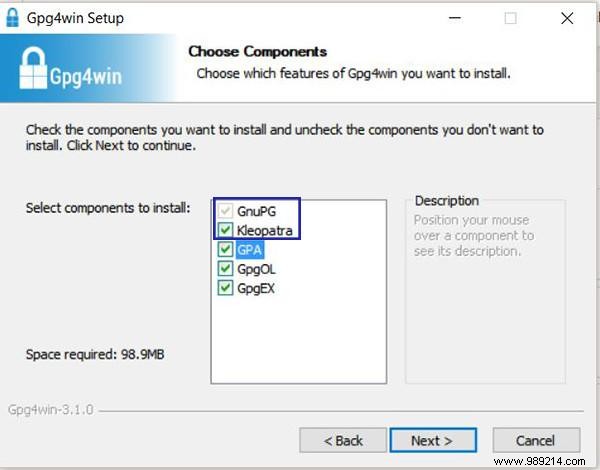
2. Install, ensuring GnuPG (core engine) and Kleopatra (intuitive GUI) are selected. Others are optional.
3. Launch Kleopatra.

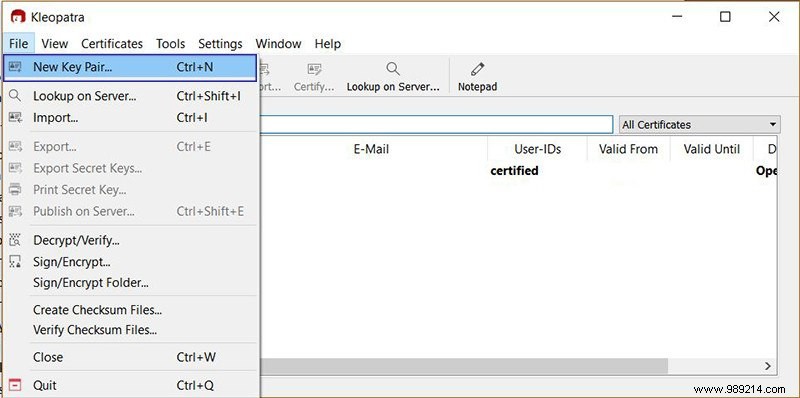
4. File > New Key Pair.
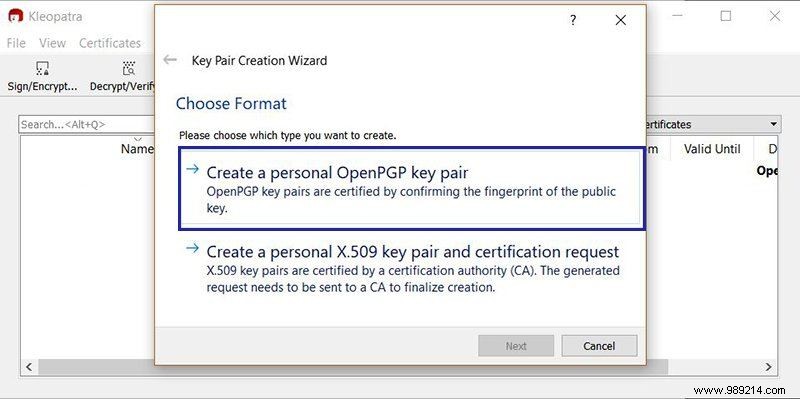
5. Choose "Create personal OpenPGP key pair."
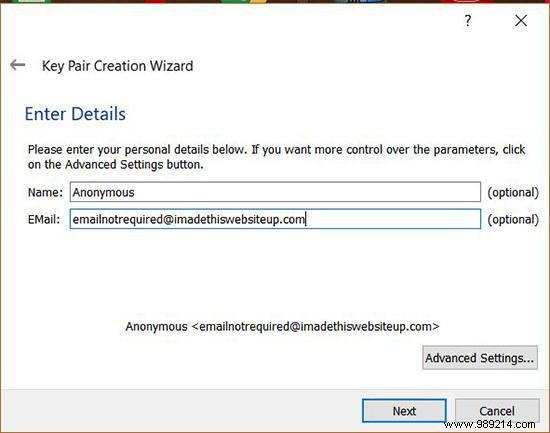
6. Optionally, add your name/email (real or alias).
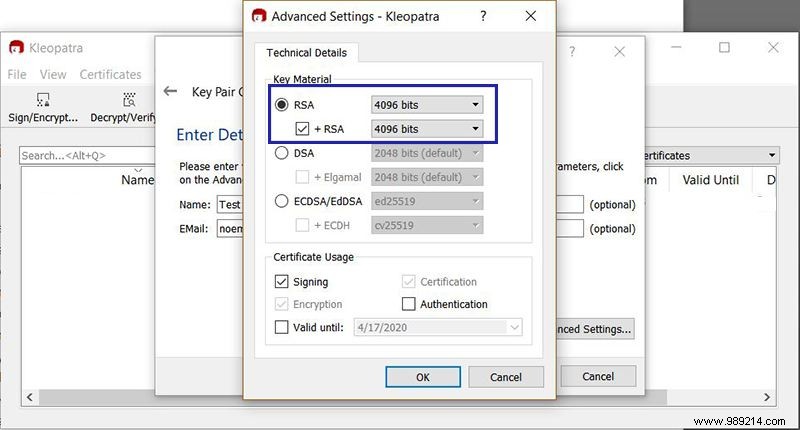
7. Advanced Settings: Select RSA, boost key size to 4096 bits for top-tier security without noticeable slowdown.
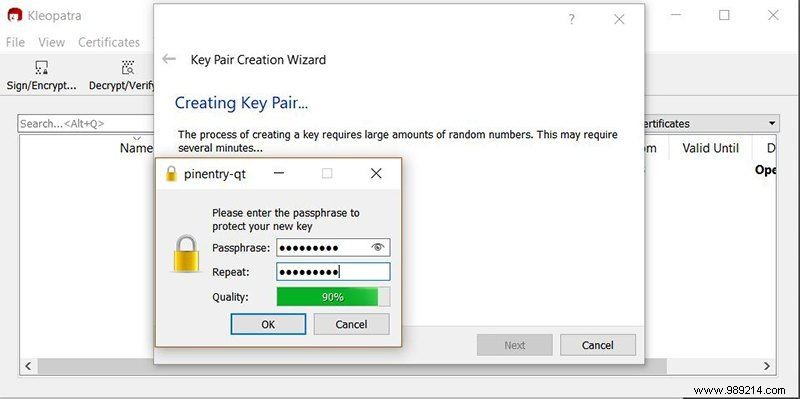
8. OK > Next. Generate passphrase—store securely, e.g., in a password manager; it's irrecoverable if lost.
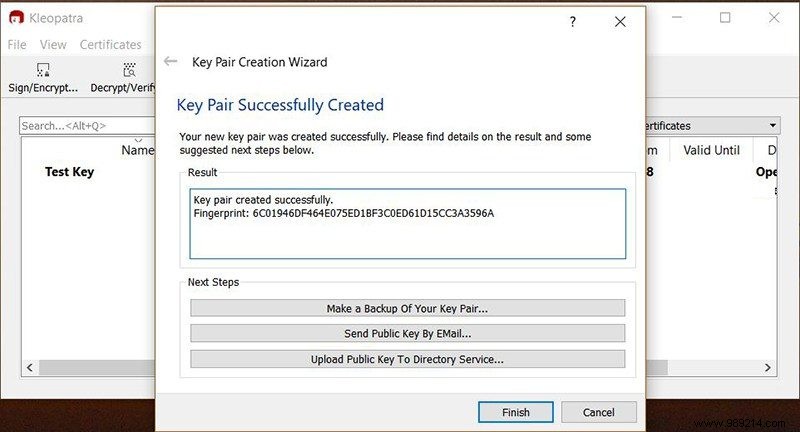
9. Keys ready! Export public key for sharing.
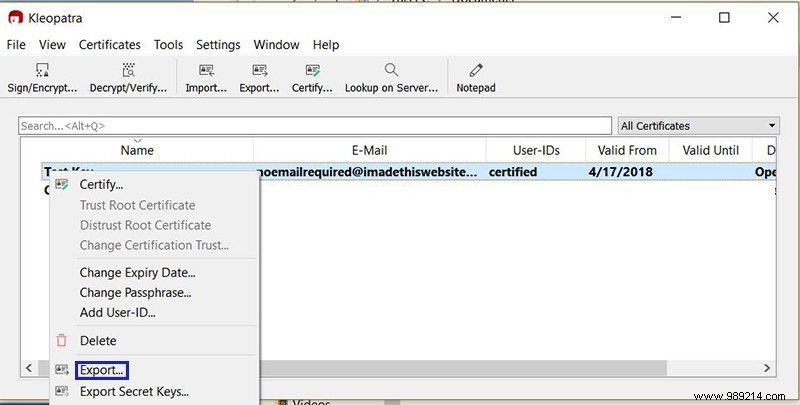
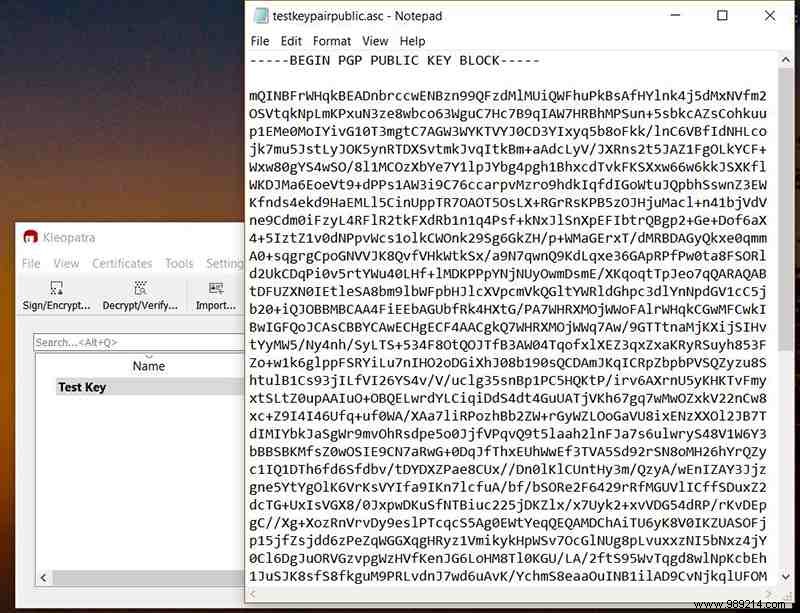
10. Right-click key > Export (ASCII-armored .asc file).
11. Save, then open in Notepad (File > Open > All Files).
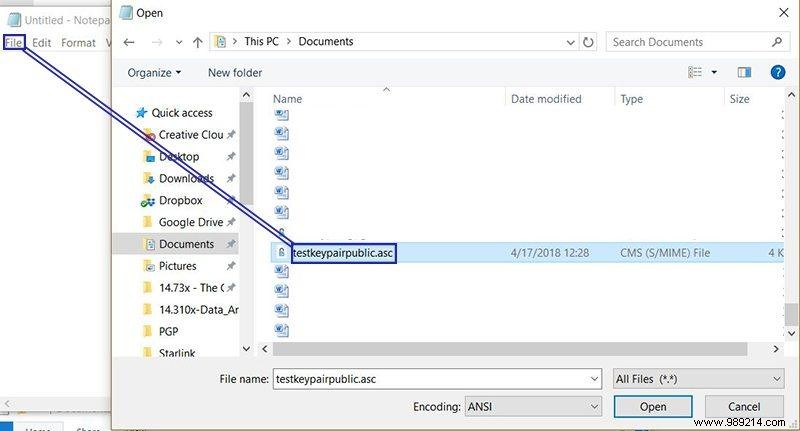
12. View your public key.
13. For private key: Right-click > Export Secret Keys. Store offline securely.
Kleopatra handles encryption/decryption natively. Test by encrypting a file with a public key and decrypting with the private.
PGP's strength hinges on private key secrecy. Compromise it, and all public-key-encrypted data is readable. Options: HDD with protections, encrypted USB, or hardware like the Lexar JumpDrive Fingerprint F35.