As cybersecurity awareness grows, attackers are getting more creative. A sophisticated new malware strain disguises itself by altering desktop shortcuts for popular apps like Chrome, Firefox, and Skype, tricking users into running malicious code. Drawing from analyses by experts like Trend Micro, we'll break down how it works and share proven protection strategies.
This malware often starts as a malicious Word macro in a seemingly innocuous document, such as a Russian file featuring a house photo—though it could hide in any file type.
Image credit: Trend Micro's analysis of the infected document.
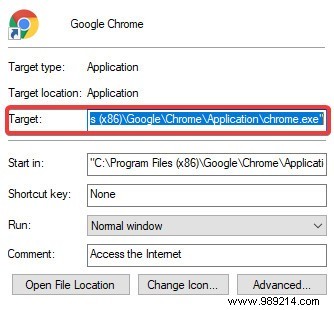
Once enabled, the macro scans the desktop for shortcuts to Chrome, Firefox, Internet Explorer, Opera, or Skype. It downloads a malicious executable, then modifies the shortcut's target to launch this file instead.
When you click the compromised shortcut, it executes the payload, downloading additional malware. This includes installing Ammyy Admin—a remote desktop tool abused by attackers for full control. It also gathers system details and sends them to the threat actor.
Avoiding shady downloads and never enabling macros from unknown sources is your first line of defense. Verify file origins and sender trust before opening attachments.
For ongoing protection, deploy reputable antivirus software. Reliable free options from trusted vendors effectively detect and block these executables, preventing damage.
If infected, right-click suspicious shortcuts, select Properties, and restore the original Target path (e.g., Chrome.exe location). Run a full antivirus scan to eliminate payloads. Awareness is key—this multi-step attack is avoidable with vigilance.
While desktop icons turning malicious is concerning, safe habits thwart it. What are your thoughts on this tactic? Share in the comments.
Image credit: Office - front