As a cybersecurity expert with years analyzing data breaches, I've seen how pervasive theft is. If you've used Yahoo, 3 billion accounts were compromised in 2013-2014. Stayed at Marriott? Up to 500 million guest records stolen from 2014-2018. Clinging to that old Hotmail or MySpace? 360 million MySpace accounts hacked. MyFitnessPal users: 150 million accounts exposed.
In these incidents, hackers grabbed emails, user info, activity logs, and more. The silver lining? Sensitive data like passwords was often encrypted—typically with AES-256. But is it truly secure?
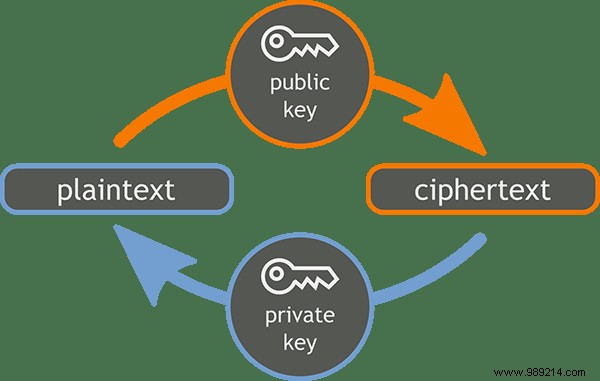
Encryption protects data by scrambling it with a key. Brute-forcing AES-256 would take 3 sextillion (3×1051) years with today's tech—practically impossible. Quantum advances may change this eventually, but for now, it's impenetrable.
Yet, encryption isn't foolproof. Attackers target the keys. Ideal security stores keys separately, encrypts them, rotates them regularly, and retrieves them securely. If a site nails this, your data stays safe. But most don't.

Reviewing those breaches:
| Breach | Year | Affected Records | Encrypted/Hashed | Plaintext Exposed |
|---|---|---|---|---|
| Yahoo | 2013-2014 | 3 billion | Hashed passwords (mostly bcrypt, some MD5) Some security questions | Names Email addresses Phone numbers Dates of birth |
| Marriott | 2014-2018 | 500 million | 8.6 million credit cards 20.3 million passports (some) | Names Addresses Dates of birth Gender Loyalty data Booking info 5.25 million passports |
| MySpace | 2016 | 360 million | Passwords (SHA-1, unsalted) | Email addresses Usernames |
| MyFitnessPal | 2018 | 150 million | Passwords (bcrypt salted, some SHA-1) | Usernames Email addresses |
Typically, only passwords (hashed, not encrypted) and payments get protection. Encrypting everything demands more resources, so plaintext PII often leaks. Even 'secure' hashes like bcrypt faltered with legacy MD5/SHA-1 or missing salts—exposing passwords outright.
Marriott's plaintext passports highlight lapses; credit cards' keys might've been grabbed too.
Rare sites like Dropbox or Google Drive encrypt files end-to-end with robust key management. There, data endures. But most breaches expose unencrypted PII or weak hashing.
You can't always avoid sharing data, but minimize it, never reuse passwords, and check Have I Been Pwned? for exposures.
Image Credits: Public Key Encryption Keys, Data Security Breach, Orange Blue Public Key Cryptography