Without modern cryptographic techniques, the Internet as we know it simply wouldn't exist. These tools enable secure communications that power everything from online banking to everyday browsing. Encryption algorithms ensure safe data exchange and reliable identity verification, forming the backbone of our connected world.
Symmetric encryption uses a single shared secret key for both encrypting and decrypting data. It's incredibly efficient for large volumes of information, making it ideal for bulk data protection. Common examples include AES (Advanced Encryption Standard), the gold standard today, and older algorithms like DES. The challenge lies in securely distributing the key to all parties without interception.
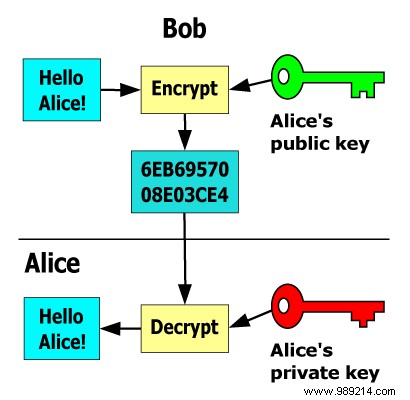
Asymmetric encryption, also known as public-key cryptography, relies on a mathematically linked pair of keys: a public key for encryption and a private key for decryption. Anyone can encrypt a message using the recipient's public key, but only the private key holder can decrypt it. This eliminates the need for shared secrets or prior trust between parties.
Consider this classic padlock analogy for Alice securely communicating with Bob:
Alice can freely distribute copies of the open padlock, allowing secure messages from anyone—provided the lock is complex enough to resist picking.
These algorithms' strength stems from 'one-way' mathematical problems that are easy to compute forward but infeasible to reverse. RSA, a cornerstone public-key system, bases its security on the difficulty of factoring the product of two massive prime numbers.
A user generates two large primes, multiplies them to form the modulus (public), and derives keys from there while keeping the primes secret (private). For RSA-1024—the former minimum standard—this involves 1024-bit products from 512-bit primes. Factoring it without the key would take about 5.95 × 10211 years, dwarfing the universe's age of roughly 13.75 × 1019 years.
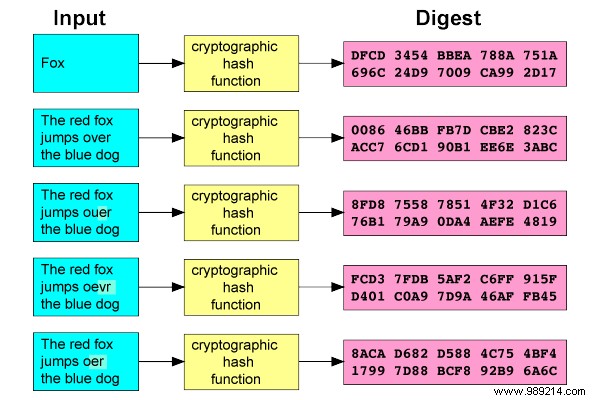
Hash functions transform any input into a fixed-length 'digest' or hash. Cryptographic hashes like SHA are deterministic—same input yields same output—and highly sensitive: a single character change drastically alters the hash. Collisions (different inputs, same hash) should be computationally impossible.
Hashes underpin digital signatures and password storage. Instead of saving plaintext passwords, servers store and compare hashes.

For password security, a unique random 'salt' is appended to the password before hashing. Identical passwords thus produce unique hashes, thwarting rainbow table attacks and dictionary assaults on breached databases.
Before the 1970s, encryption relied solely on symmetric keys. The public-key breakthrough proved two distinct keys could enable encryption and decryption without shared secrets or trust—a revolution that birthed the secure Internet. Today, banking, shopping, messaging, and browsing all depend on these techniques.